- Main
- Computers - Networking
- Penetration Testing: A Hands-On...

Penetration Testing: A Hands-On Introduction to Hacking
Georgia Weidman이 책이 얼마나 마음에 드셨습니까?
파일의 품질이 어떻습니까?
책의 품질을 평가하시려면 책을 다운로드하시기 바랍니다
다운로드된 파일들의 품질이 어떻습니까?
Penetration testers simulate cyber attacks to find security weaknesses in networks, operating systems, and applications. Information security experts worldwide use penetration techniques to evaluate enterprise defenses. In Penetration Testing, security expert, researcher, and trainer Georgia Weidman introduces you to the core skills and techniques that every pentester needs. Using a virtual machine–based lab that includes Kali Linux and vulnerable operating systems, you’ll run through a series of practical lessons with tools like Wireshark, Nmap, and Burp Suite. As you follow along with the labs and launch attacks, you’ll experience the key stages of an actual assessment—including information gathering, finding exploitable vulnerabilities, gaining access to systems, post exploitation, and more.
Learn how to:
- Crack passwords and wireless network keys with brute-forcing and wordlists
- Test web applications for vulnerabilities
- Use the Metasploit Framework to launch exploits and write your own Metasploit modules
- Automate social-engineering attacks
- Bypass antivirus software
- Turn access to one machine into total control of the enterprise in the post exploitation phase
You’ll even explore writing your own exploits. Then it’s on to mobile hacking—Weidman’s particular area of research—with her tool, the Smartphone Pentest Framework. With its collection of hands-on lessons that cover key tools and strategies, Penetration Testing is the introduction that every aspiring hacker needs.
Learn how to:
- Crack passwords and wireless network keys with brute-forcing and wordlists
- Test web applications for vulnerabilities
- Use the Metasploit Framework to launch exploits and write your own Metasploit modules
- Automate social-engineering attacks
- Bypass antivirus software
- Turn access to one machine into total control of the enterprise in the post exploitation phase
You’ll even explore writing your own exploits. Then it’s on to mobile hacking—Weidman’s particular area of research—with her tool, the Smartphone Pentest Framework. With its collection of hands-on lessons that cover key tools and strategies, Penetration Testing is the introduction that every aspiring hacker needs.
카테고리:
년:
2014
판:
1
출판사:
No Starch Press
언어:
english
페이지:
528
ISBN 10:
1593275641
ISBN 13:
9781593275648
파일:
PDF, 11.74 MB
개인 태그:
IPFS:
CID , CID Blake2b
english, 2014
파일이 귀하의 이메일로 송부 됩니다. 1-5분 소요됩니다.
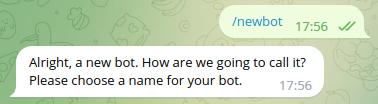
1~5분 이내로 파일이 사용자님의 Telegram 계정으로 전송될 것입니다.
주의: 자신의 계정이 Z-Library Telegram 봇과 연결되어 있는지 확인하십시오.
1~5분 이내로 파일이 사용자님의 Kindle 기기로 전송될 것입니다.
비고: Kindle로 보내시는 책은 모두 확인해 보실 필요가 있습니다. 메일함에 Amazon Kindle Support로부터 확인 메일이 도착했는지 메일함을 점검해 보시기 바랍니다.
로의 변환이 실행 중입니다
로의 변환이 실패되었습니다
주로 사용되는 용어
연결된 도서 목록



























































































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  파일을 변환하실 수 있습니다
파일을 변환하실 수 있습니다  더 많은 검색 결과
더 많은 검색 결과 기타 혜택
기타 혜택